
A financially motivated cybergang tracked by Mandiant as ‘UNC3944’ is using phishing and SIM swapping attacks to hijack Microsoft Azure admin accounts and gain access to virtual machines. From there, the attackers abuse the Azure Serial Console to install remote management software for persistence and abuse Azure Extensions for stealthy surveillance.
Mandiant reports that UNC3944 has been active since at least May 2022, and their campaign aims at stealing data from victim organizations using Microsoft’s cloud computing service.
UNC3944 was previously attributed to creating the STONESTOP (loader) and POORTRY (kernel-mode driver) toolkit to terminate security software.
The threat actors utilized stolen Microsoft hardware developer accounts to sign their kernel drivers.
SIM swapping Azure admins
The initial access to the Azure administrator’s account takes place using stolen credentials acquired in SMS phishing, a common tactic of UNC3944.
Next, the attackers impersonate the administrator when contacting help desk agents to trick them into sending a multi-factor reset code via SMS to the target’s phone number.
However, the attacker had already SIM-swapped the administrator’s number and ported it to their device, so they received the 2FA token without the victim realizing the breach.
Mandiant has yet to determine how the hackers perform the SIM swapping phase of their operation. However, previous cases have shown that knowing the target’s phone number and conspiring with unscrupulous telecom employees is enough to facilitate illicit number ports.
Once the attackers establish their foothold in the targeted organization’s Azure environment, they use their administrator privileges to gather information, modify existing Azure accounts as needed, or create new ones.
Living off the Land tactics
In the next attack phase, UNC3944 uses Azure Extensions to conduct surveillance and gather information, mask their malicious operations as seemingly innocuous daily tasks, and blend with regular activity.
Azure Extensions are “add-on” features and services that can be integrated into an Azure Virtual Machine (VM) to help expand capabilities, automate tasks, etc.
Because these extensions are executed inside the VM and are typically used for legitimate purposes, they’re both stealthy and less suspicious.
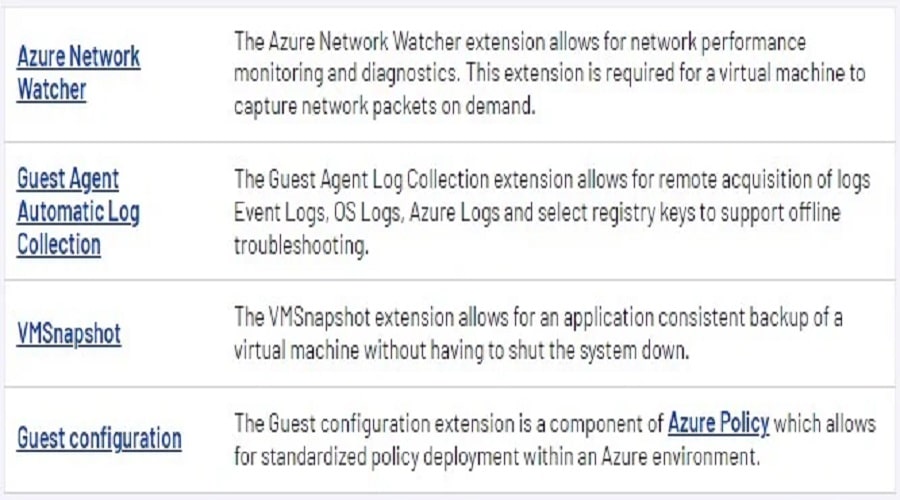
In this case, the threat actor abused the built-in Azure diagnostic extensions like “CollectGuestLogs,” which was leveraged for gathering log files from the breached endpoint. Additionally, Mandiant has found evidence of the threat actor attempting to abuse the following additional extensions:
Breaching VMs to steal data
Next, UNC3944 uses Azure Serial Console to gain administrative console access to VMs and run commands on a command prompt over the serial port.
“This method of attack was unique in that it avoided many of the traditional detection methods employed within Azure and provided the attacker with full administrative access to the VM,” explains Mandiant’s report.
Mandiant noticed that “whoami” is the first command the intruders execute to identify the currently logged-in user and gather enough information to further the exploitation.
More information on how to analyze logs for Azure Serial Console can be found in the reports appendix.
Next, the threat actors use PowerShell to enhance their persistence on the VM and install multiple commercially available remote administrator tools not named in the report.
“To maintain presence on the VM, the attacker often deploys multiple commercially available remote administration tools via PowerShell,” reads Mandiant’s report.
“The advantage of using these tools is that they’re legitimately signed applications and provide the attacker remote access without triggering alerts in many endpoint detection platforms.”
The next step for UNC3944 is to create a reverse SSH tunnel to their C2 server, to maintain stealthy and persistent access via a secure channel and bypass network restrictions and security controls.
The attacker configures the reverse tunnel with port forwarding, facilitating a direct connection to Azure VM via Remote Desktop. For example, any inbound connection to remote machine port 12345 would be forwarded to the local host port 3389 (Remote Desktop Protocol Service Port).
Finally, the attackers use the credentials of a compromised user account to log in to the compromised Azure VM via the reverse shell and only then proceed to expand their control within the breached environment, stealing data along the way.
The attack presented by Mandiant demonstrates UNC3944’s deep understanding of the Azure environment and how they can leverage built-in tools to evade detection.
When this technical know-how is combined with high-level social engineering skills that help the attackers perform SIM swapping, the risk is magnified.
At the same time, a lack of understanding of cloud technologies from organizations that deploy insufficient security measures, such as SMS-based multi-factor authentication, creates opportunities for these sophisticated threat actors.
Source: www.bleepingcomputer.com



