A new ransomware operation named ‘0mega’ targets organizations worldwide in double-extortion attacks and demands millions of dollars in ransoms.
0mega (spelled with a zero) is a new ransomware operation launched in May 2022 and has attacked numerous victims since then.
What we know about 0mega
A ransomware sample for the 0mega operation hasn’t yet been found, therefore there’s not much information on how files are encrypted.
However, we do know that the ransomware appends the .0mega extension to the encrypted file’s names and creates ransom notes named DECRYPT-FILES.txt.
These ransom notes are customized per victim, usually containing the company name and describing the different types of data stolen in attacks. In addition, some notes include threats on how the 0mega gang will disclose the attack to business partners and trade associations if a ransom is not paid.
These ransom notes include a link to a Tor payment negotiation site with a “support” chat that victims can use to contact the ransomware gang.
To log in to this site, victims must upload their ransom notes that include a unique Base64-encoded blob used by the site to identify the victim.
Dedicated 0mega data leak site
Like almost all enterprise-targeting ransomware operations, 0mega runs a dedicated data leak site that the threat actors use to publish stolen data if a ransom is not paid.
0mega’s leak site is currently hosting 152 GB of data stolen from an electronics repair company in a May attack.
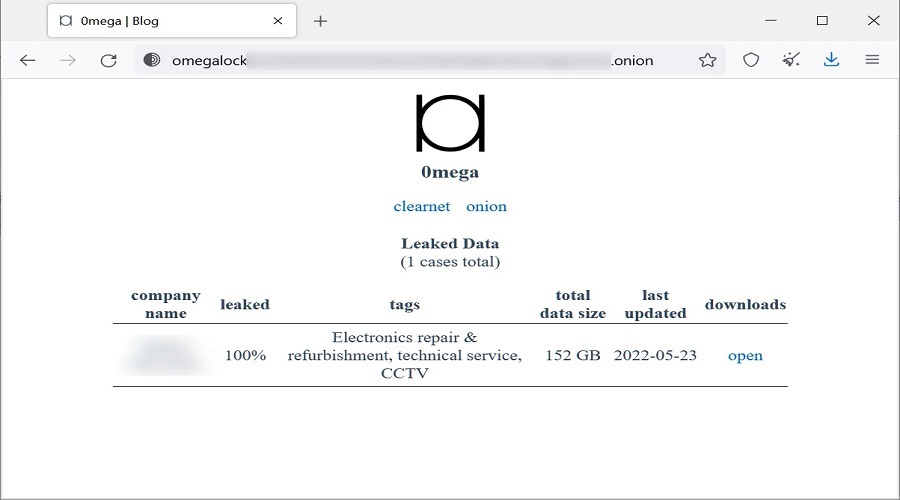
However, last week there was an additional victim that has since been removed, indicating that the company may have paid a ransom.
As this is a relatively new operation, we will likely see more attacks in the future, and it is one we need to keep an eye on.
Source: www.bleepingcomputer.com